Part 2: Attack Simulation from Another VM & Attacker's Log Inspection (Failed Authentication and Log Observation), by Duyet Bui
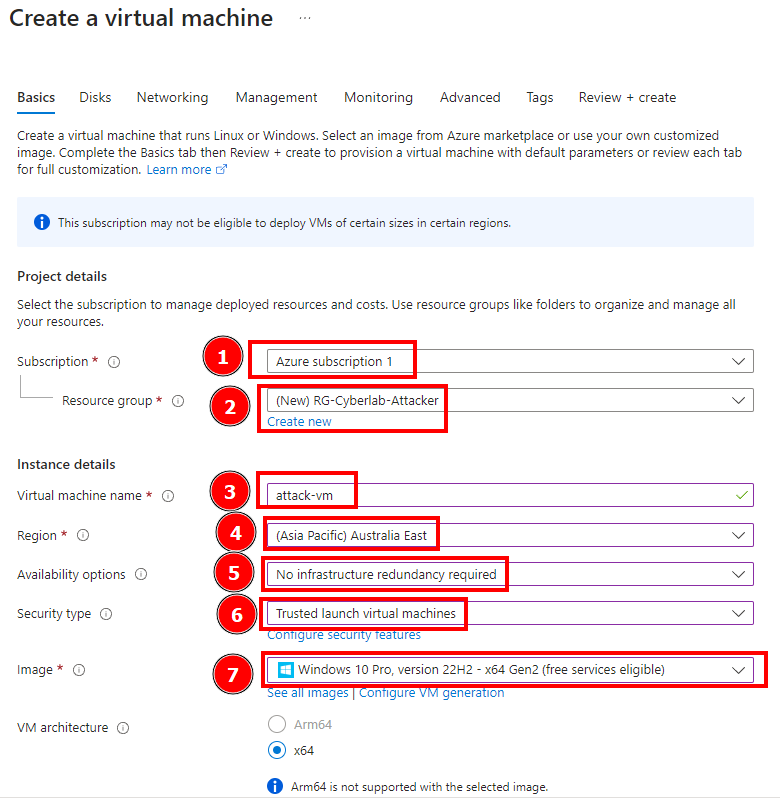
In this session we’re going to simulate an attack from another VM and then observe the attacker’s log. First we create an attacker VM. This VM’s name is attack-vm and also contain a different…

Part 9: Microsoft Sentinel Incident Response., by Duyet Bui

What are breach and attack simulations? - IBM Blog
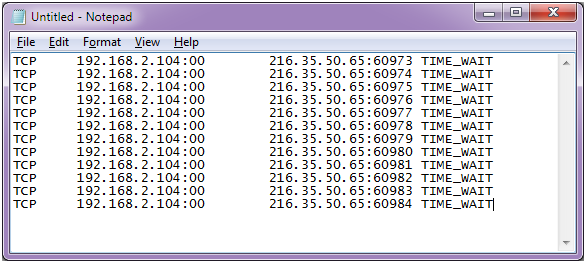
How to Detect and Analyze DDoS Attacks Using Log Analysis
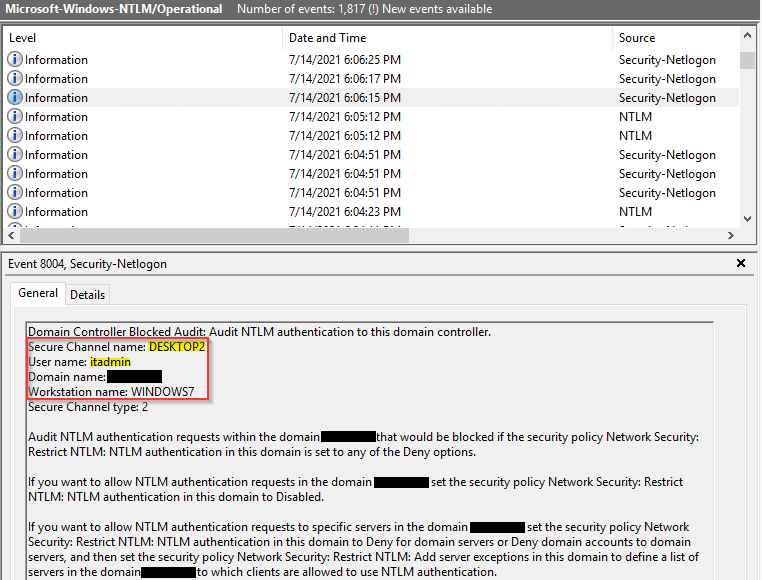
How to Investigate NTLM Brute Force Attacks
Part 5: Configuring/Collection Windows Security Event Logs and Syslog Logs and for Log Analytics Workspace., by Duyet Bui

Portswigger: Exploiting vulnerabilities in LLM APIs

Part 1: Create Windows 10 Pro Virtual Machine and Install SQL Server and Create Vulnerabilities, by Duyet Bui

100 million RPS DDoS attack exploits HTTP/2 Rapid Reset Flaw

PDF) Towards Automated Attack Simulations of BPMN-based Processes
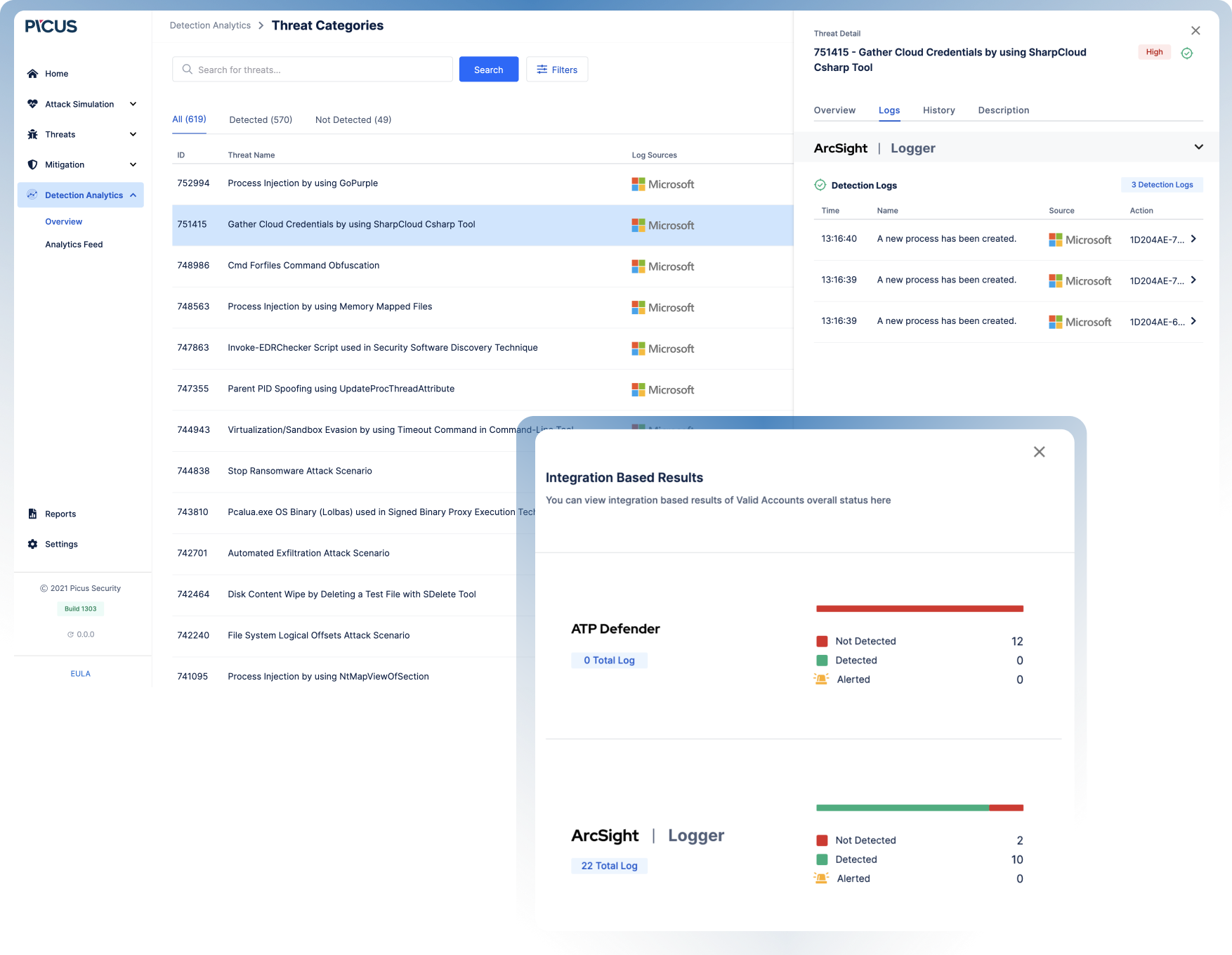
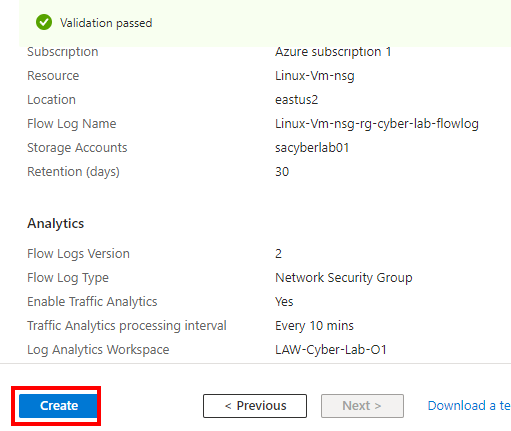
Log Validation with Attack Simulation

Detection, differentiation and localization of replay attack and false data injection attack based on random matrix